Trezor Login: Securely Access Your Crypto Wallet
Learn how to safely log in to your Trezor device and manage your digital assets confidently.
What Is Trezor Login?
Trezor Login is the process of securely accessing your Trezor hardware wallet through Trezor Suite or supported web interfaces. Unlike conventional password logins, Trezor uses hardware authentication to keep your private keys offline, protecting your crypto from malware and hackers.
This guide will walk you through beginner-friendly steps, highlight security best practices, and explain intermediate scenarios for multi-account and DeFi access.
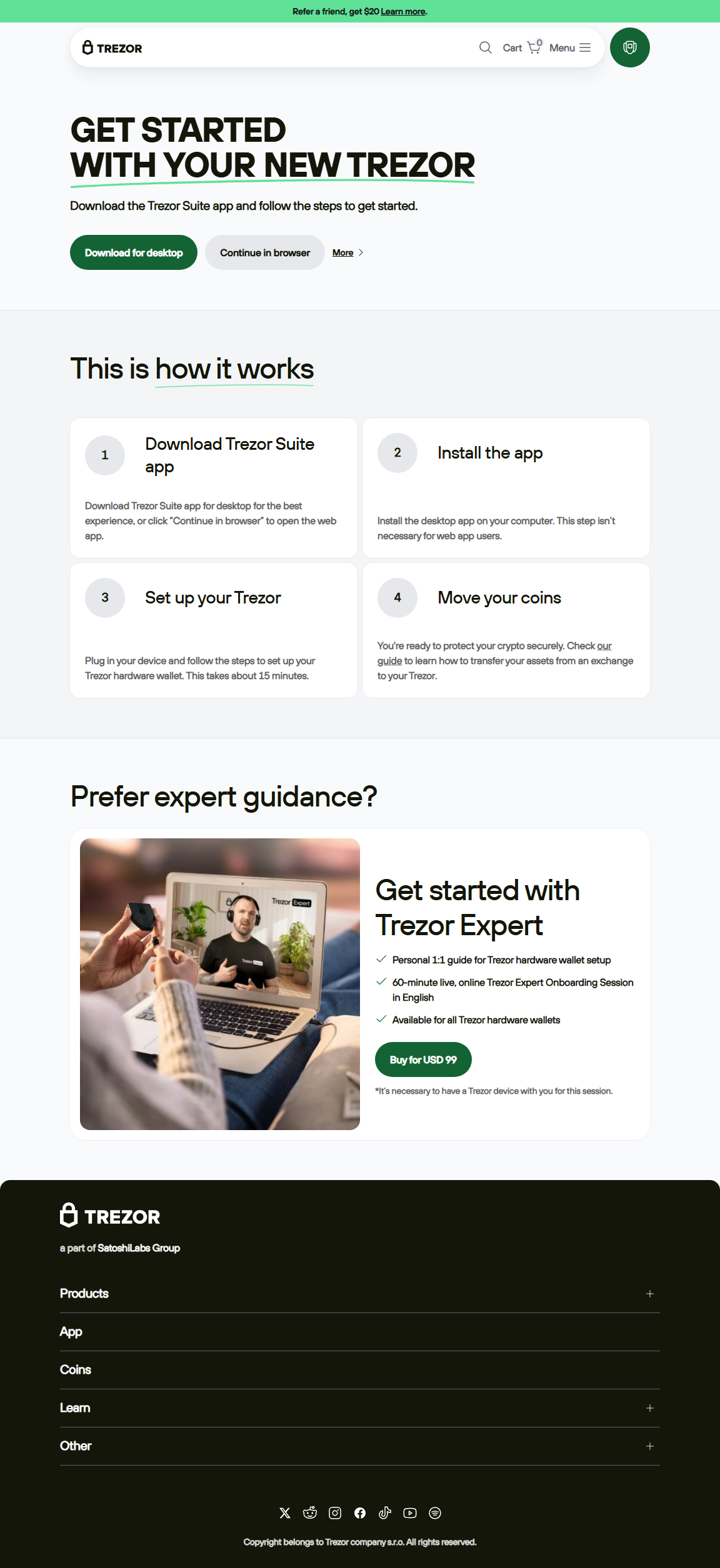
Step-by-Step Trezor Login
Step 1: Connect Your Device
Plug your Trezor hardware wallet into your computer or mobile device using a USB cable. Verify that your firmware is up-to-date to prevent security vulnerabilities.
Step 2: Open Trezor Suite
Launch the official Trezor Suite app. Always confirm you are using the official software to avoid phishing attempts.
Step 3: Enter Your PIN
Enter your unique PIN directly on the Trezor device. This ensures your private keys remain offline, even if your computer is compromised.
Step 4: Access Your Wallet
After PIN confirmation, you can access your wallet to view balances, send or receive crypto, and connect to supported DeFi apps and NFT marketplaces safely.
🔒 Trezor Login Security Best Practices
- Always use official Trezor Suite or verified web portals.
- Never input your recovery seed online.
- Confirm all transactions directly on the Trezor device.
- Keep firmware and software up-to-date.
- Be cautious of phishing websites, emails, and third-party apps.
Common Login Scenarios
Logging in After a Device Reset
If your Trezor has been reset, restore it using your recovery seed before logging in with your PIN.
Switching Between Multiple Wallets
Trezor Suite supports multiple accounts, allowing you to toggle wallets without disconnecting your device.
DeFi and NFT Access
When logging in to DeFi apps or NFT marketplaces, always confirm prompts directly on the device to maintain security.
Trezor Login vs Traditional Wallet Logins
| Feature | Trezor Login | Traditional Wallet Login |
|---|---|---|
| Private Key Storage | Offline on device | Online/software-based |
| Security Against Hacks | High, hardware-based | Moderate |
| Ease of Use | Moderate, requires device | High, software-only |
Frequently Asked Questions
What do I need for Trezor Login?
A Trezor hardware wallet, Trezor Suite, and your device PIN.
Can I log in from multiple devices?
Yes, using your recovery seed and PIN, you can access your wallet on multiple devices.
Is Trezor Login safe?
Yes, private keys remain offline on the hardware wallet, offering superior security.
What if I forget my PIN?
If you forget your PIN, you can reset the device and restore your wallet using your recovery seed.
Final Thoughts
Trezor Login provides a secure and reliable method to access your cryptocurrency safely. By following best practices and using official software, you can confidently manage your assets while participating in DeFi, NFTs, and multi-account management.
Always verify official channels and confirm all actions on your Trezor device for maximum security.